The DOJ’s new Data Security Program isn’t coming, it’s here. Within its first 180 days, the rule governing bulk data transfers has moved from policy blueprint to active enforcement reality. If your organization handles sensitive personal data and works with foreign entities, this regulation demands your attention now.
Here’s what’s changed, what regulators expect, and what your business needs to do about it.
What Is the DOJ Bulk Data Transfers Rule?
At its core, the DOJ bulk data transfers rule codified at 28 CFR Part 202 is designed to stop adversarial governments from getting their hands on large-scale datasets belonging to Americans. We’re talking about health records, financial data, geolocation information, biometric identifiers, and genomic data — the kind of information that, in the wrong hands, could be used to track individuals, train AI models, or gain strategic intelligence.
The rule was born from Executive Order 14117, which directed the Department of Justice to build a regulatory program specifically targeting cross-border data risks tied to national security. The result is the Data Security Program, enforced by DOJ’s National Security Division.
Six countries are currently designated as “countries of concern”: China (including Hong Kong and Macau), Russia, Iran, North Korea, Cuba, and Venezuela. But the rule doesn’t stop at government-to-government transfers. It also targets covered persons, individuals and entities with ties to those countries, even when a transaction looks like a routine commercial deal on the surface.
Why This Rule Exists and Why It Matters Now
For years, the U.S. relied on a patchwork of sector-specific privacy laws, export controls, sanctions, and CFIUS reviews to manage data security. That approach had blind spots big ones. Data brokers could sell bulk datasets to foreign buyers through commercial contracts that never triggered a national security review. Offshore service centers could access sensitive records without anyone raising a flag.
The explosion of cloud computing, cross-border analytics, and global outsourcing made those gaps impossible to ignore. Adversarial governments didn’t need to hack their way into sensitive databases when they could simply buy the data or access it through legitimate-looking supply chain relationships.
The DOJ bulk data transfers rule closes that door. It shifts the U.S. from a reactive, transaction-by-transaction approach to a proactive control regime that regulates entire categories of data and deal structures. Think of it as export controls, but for sensitive personal data.
For businesses that previously thought of data transfers as purely a privacy or compliance issue, the message from the first 180 days is unmistakable: national security is now a central pillar of U.S. data policy, and the enforcement expectations match.
How the Rule Works: Prohibited vs. Restricted Transactions
Not all cross-border data deals are treated equally under this framework. The rule draws a clear line between two categories.
Prohibited transactions are completely off-limits. These include certain data brokerage arrangements with countries of concern or covered persons, as well as transactions involving access to bulk human genomic data or biospecimens above defined thresholds. No amount of contractual safeguards can make these permissible.
Restricted transactions can move forward but only if you meet strict conditions. Vendor agreements, employment arrangements, and investment deals may qualify as restricted transactions, meaning they require robust due diligence, contractual controls, audit mechanisms, and detailed documentation before they can proceed.
The distinction matters enormously. Getting it wrong treating a prohibited transaction as merely restricted, or failing to implement required safeguards for a restricted one — creates serious legal exposure.
Who’s Affected? More Businesses Than You Think
If you’re assuming this rule only applies to defense contractors and big tech companies, think again. The DOJ bulk data transfers framework reaches across a wide range of industries:
- Healthcare and life sciences organizations handling patient records, clinical trial data, or genomic information
- Financial services firms processing large volumes of consumer financial data
- Cloud providers and SaaS platforms that store or process sensitive data for clients
- Data brokers and adtech companies that aggregate and sell consumer data
- Any global business with shared service centers, offshore development teams, or foreign vendor relationships
Even if your company has no direct operations in a country of concern, you’re not off the hook. The rule focuses on access, not just transfers. If a subcontractor’s offshore team can query a database containing bulk sensitive data, that could qualify as a covered data transaction.
What Changed in the First 180 Days
The rule rolled out on a staggered timeline, and the first 180 days have already reshaped how businesses approach cross-border data flows.
April 8, 2025 marked the effective date for most prohibitions and restrictions. A 90-day grace period followed, during which the DOJ signaled it would not prioritize civil enforcement against organizations making good-faith compliance efforts. That window closed in early July.
Since then, the enforcement posture has shifted. While criminal enforcement for egregious violations was always on the table, the expectation is now clear: by mid-2025 and beyond, organizations will be held to a higher standard. Additional compliance milestones including due diligence, audit, and reporting obligations kicked in through October 2025, with further reporting mandates extending into 2026.
Industry response has been intense. Multinational technology, cloud, and life sciences companies have stood up cross-functional task forces combining legal, security, privacy, and engineering teams. Advisory firms report surging demand for gap assessments and regulatory mapping. Some organizations have taken a conservative approach, preemptively cutting ties with entities in countries of concern or restructuring deals to exclude high-risk data categories entirely.
The Compliance Roadmap: What You Actually Need to Do
Meeting the requirements of the DOJ bulk data transfers rule isn’t a one-time checklist exercise. It’s an ongoing governance discipline that touches legal, technical, and operational functions across your organization.
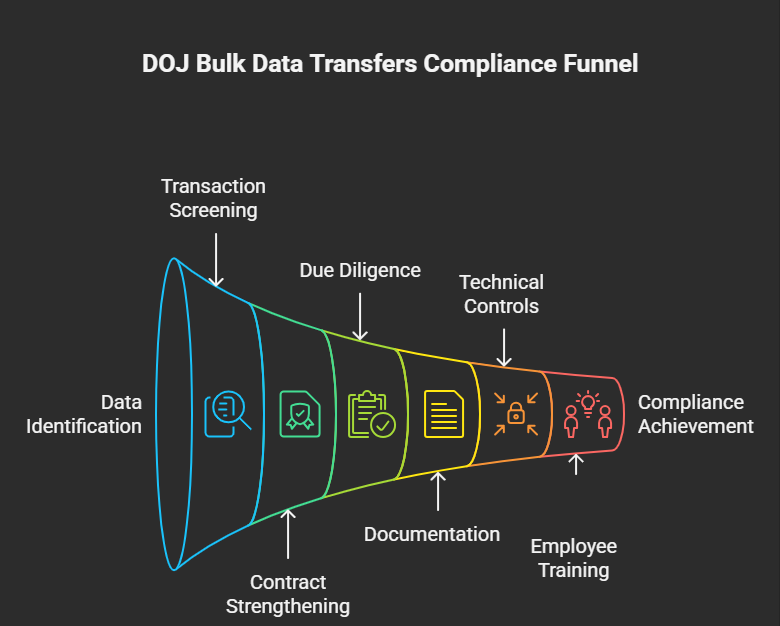
Map Your Data Flows
Start with a comprehensive inventory. Where does your sensitive personal data live? Who has access to it? Does it cross borders directly or through cloud infrastructure, vendor relationships, or employee access? You need to classify data by category and volume, then determine whether any transfers or access arrangements hit the bulk thresholds defined in the rule.
This foundational step is non-negotiable. You can’t assess your risk if you don’t know where your data goes.
Screen Every Transaction
Build processes to identify data brokerage, vendor, employment, and investment agreements that involve foreign persons especially those connected to countries of concern or fitting the definition of covered persons. Centralized review mechanisms, typically housed within legal or compliance teams, should evaluate whether these agreements create pathways to bulk sensitive data and whether they can be structured as permissible restricted transactions or must be declined.
Strengthen Your Contracts
For restricted transactions, your agreements need teeth. Contracts must include provisions that prohibit onward transfer or resale of regulated data to countries of concern or covered persons. They should also include audit rights, data localization clauses, subcontractor controls, and clear remedies for violations.
This isn’t just a legal department task. Procurement and business development teams need to understand that deviating from standard contractual language can trigger heightened legal review under the framework.
Conduct Rigorous Due Diligence
Risk-based assessments of counterparties are essential for restricted transactions. You’ll need to evaluate ownership structures, governance, location, workforce composition, and technical environments to determine whether a transaction could realistically enable a country of concern or covered person to access bulk sensitive data.
In practice, this often means enhanced know-your-customer checks, beneficial ownership analysis, scrutiny of offshore staffing models, and evaluation of a partner’s own data security posture.
Document Everything
The rule requires detailed records covering the nature of covered data transactions, data categories and volumes, counterparty characteristics, and the rationale behind classification decisions. In some cases, you must report certain restricted transactions or rejected prohibited transactions directly to the DOJ.
Weak documentation is one of the fastest ways to undermine a good-faith compliance defense. If regulators come knocking, your records need to tell a clear story.
Deploy Technical Controls
Legal safeguards alone aren’t enough. Organizations are increasingly implementing data segmentation, role-based access controls, data loss prevention tools, and geo-fencing to ensure regulated datasets can’t be reached from countries of concern or by covered persons. Separate environments for sensitive data, privacy-enhancing technologies, and restricted cross-border replication are all becoming standard practice.
Train Your People
Employees in vendor management, procurement, HR, R&D, and M&A need to understand the basics: what triggers a covered data transaction, why bulk thresholds matter, and when to escalate potential issues. Organizations that treat this as a narrow legal concern confined to a small team will inevitably miss risk indicators buried in everyday business decisions.
The smartest approach is to integrate DOJ bulk data transfers training into existing export control or sanctions compliance programs, leveraging governance structures your teams already know.
Common Mistakes to Avoid
Early implementation has revealed several recurring pitfalls that trip up even well-resourced organizations:
Assuming no direct country-of-concern relationship means no risk. Ownership structures, data routing paths, and offshore staffing models can place regulated data within reach of covered persons even when your direct counterparty looks clean.
Relying on privacy classifications that don’t align with the rule. The DOJ’s definitions of sensitive personal data don’t map neatly onto GDPR categories or HIPAA designations. You need to assess data against the rule’s specific definitions and thresholds.
Ignoring cumulative volume. The bulk thresholds are measured over a rolling twelve-month period. A series of small transfers to the same counterparty can collectively cross the line.
Overlooking indirect access. Subcontractors, offshore support teams, and remote employees with database access can create covered data transactions that aren’t visible in standard vendor reviews.
Treating compliance as a one-time project. Business relationships and data flows evolve constantly. Your monitoring systems need to keep pace.
What Comes Next
The first 180 days have set the tone, but the regulatory landscape will continue to evolve. Expect continued refinement of guidance from the DOJ, potential changes to country-of-concern designations or bulk thresholds, and a gradual shift from cooperative engagement toward more assertive enforcement as the program matures.
Organizations that build flexible, sustainable compliance programs now will be far better positioned than those scrambling to catch up after an enforcement action makes headlines.
The bottom line: DOJ bulk data transfers compliance isn’t a side project — it’s a core governance obligation that belongs alongside your export control, sanctions, and cybersecurity programs. The businesses that recognize this early will protect themselves not just from penalties, but from the operational disruption and reputational damage that come with getting it wrong.
Frequently Asked Questions
Who needs to worry about this rule?
Any organization that collects or processes large volumes of sensitive personal or government-related data and shares it with foreign entities should assess their exposure. This includes technology companies, healthcare providers, financial institutions, cloud platforms, data brokers, and global service organizations. Even companies without direct operations in countries of concern need to evaluate whether indirect access paths exist through vendors, subcontractors, or staffing arrangements.
How do I know if my transaction is covered?
A transaction may be covered if it involves bulk U.S. sensitive personal data or government-related data, meets or exceeds the applicable volume threshold over the preceding twelve months, and gives a foreign person, country of concern, or covered person access through a data brokerage, vendor, employment, or investment agreement. Structured data-mapping and transaction screening are the most reliable way to make this determination.
What should we prioritize in the first year?
Focus on data-flow mapping, building a formal review process for cross-border arrangements, updating contracts to address onward transfer risks, conducting risk-based due diligence on foreign counterparties, and maintaining thorough records of your decision-making. Documenting your remediation steps during this early period will be critical for demonstrating good faith if questions arise later.
Does this replace existing privacy and export control obligations?
No. The DOJ bulk data transfers rule operates alongside existing privacy laws, cybersecurity requirements, and export controls not as a replacement. You’ll need to continue meeting those obligations while layering on the new requirements related to bulk thresholds, covered persons, and transactional structures. A unified governance model that coordinates across these frameworks will help reduce duplication and prevent gaps.
Are purely domestic transactions affected?
Generally, no. The rule targets access by countries of concern and covered persons, so domestic transactions between U.S. entities that don’t create such access pathways fall outside its scope. However, you should verify that domestic arrangements don’t indirectly enable foreign access through subcontracting, data routing, or downstream cross-border transfers.
What are the biggest compliance mistakes companies are making?
The most common errors include assuming that the absence of a direct relationship with a country of concern eliminates risk, failing to track cumulative data volumes over time, overlooking access by offshore support teams, and relying on privacy frameworks that don’t align with the rule’s specific definitions. Treating this as a one-off compliance exercise rather than an ongoing governance program is another frequent and costly misstep.

